Continuing improvements in security reporting add value regularly for Kurtosys customers
At Kurtosys, information security is part of our culture, and this benefits our customers in myriad ways.
Our security team is actively involved in internal processes and plays a significant role in communicating with our customers. We take pride in our ISO 27001 certification, the international standard for information security management systems, and are committed to year-on-year enhancements.
As we have made these improvements over the last decade and more, we have used them to support our technology advancements in many areas, including datacentre hosting choices, business continuity plans, and data processing compliance.
Recently, we added our Information Security Operations Centre (ISOC) team, which is dedicated to improving our security controls and ensuring they get used to maximum effect.
ISOC brings two benefits to you, our customers
First, it supports your supplier risk management process. By reporting security information related to our platform, we reduce the work you need to do in looking for potential problems. Our reports show what problems we are aware of and how we are addressing them, to minimize the stones you need to look under. This can also enable upstream reporting to regulators and auditors.
Second, ISOC helps you measure status and trends in your digital strategy. Our security information will integrate with other information to complete a picture of use and correlate intended and nefarious traffic patterns. This information improves decisions and reduces the need for targeted interventions.

How our reporting works
Our security team runs a comprehensive reporting process that ensures information is not ignored or overlooked. We report at three levels: summary for management information; extended to support investigation; and detailed to provide analysis, recommendations and conclusions.
Internally, we summarize the platform status with a weekly management report. We make weekly and monthly extended reports available to other teams to support their processes. Periodic audits and assessments provide the whole organization with measurements of their status and progress, all of which support awareness, higher standards, and best practices.
Customer information
But our reporting is not solely for internal consumption. All our customers are also interested in this security information. Every customer does some due diligence to measure and mitigate supply chain risk. Ongoing considerations are dynamic to show risk management is being improved. Our reporting initiatives play a significant role here.
Our external reporting to customers started many years ago and addressed some basic concerns, such as ‘are you updating the applications to address vulnerabilities (patching), and is there a business continuity plan?’
To that end, we have always conducted an annual penetration test, performed by a third party with a remediation plan where appropriate. Customers can supplement this with their own tests as appropriate.
We also conduct an annual disaster recovery test on our datacentre operations to confirm our service level commitments and show our business continuity plan is operational.
More recently, we also started producing additional monthly reports for customers. These contain the same sort of information we review internally but summarized differently. The current report looks at three areas.
Overall security posture
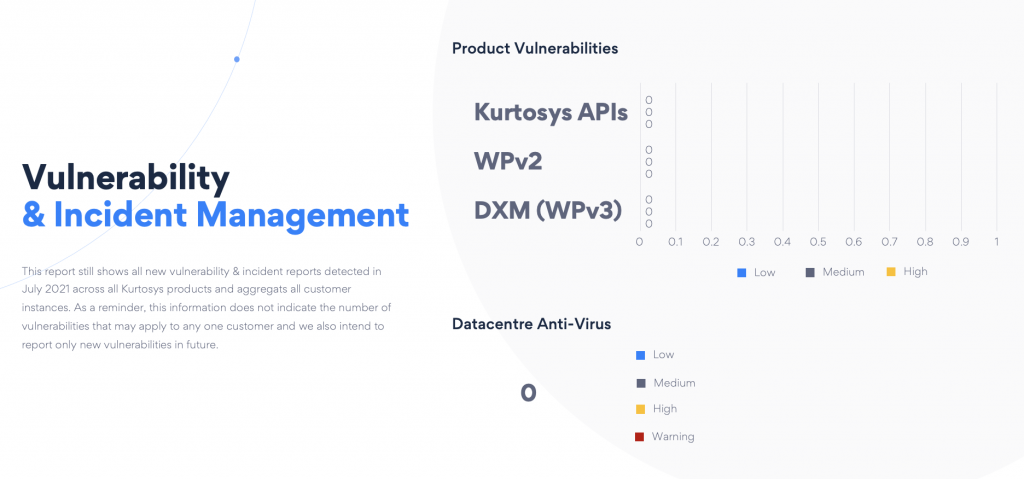
Vulnerability and incident management
These two aspects of our security policy ensure we check our apps routinely for vulnerabilities and record and report issues that impact the security and operation of our platform. Both ensure that we apply routine patching, and the detailed reporting enables us to determine trends and the impact of lessons learnt.
Web application firewall (WAF) statistics
The introduction of WAF and distributed denial of service (DDoS) attack protection seven years ago has significantly changed the way we protect against and detect security incidents. It also helps with many business problems such as improved browsing performance for customer clients using edge caching. Our reporting shows how much traffic we are processing, what sort of bad bot and other malicious activities are being blocked, and the locations and browsers requesting content.
All this work will continue to expand and match the expectations of our customers. We are also working on more customized reporting to address the different types of customer implementations on our platform. Listening to you, our customer, and providing this transparency will help reduce risk and improve trust in our solutions.
For further information, please reach out by leaving your details and someone from our Information Security team will get back to you. Alternatively, you can request a demo of how our tools and services can add value to your digital transformation.